
Neehack Inc, is a company that mainly focuses on Cyber Security. Our services are considered to be the best and affordable.
We are experts in building and securing using artificial intelligence. An active community in cyber security. Our free tools are used world-wide for security assessments purposes.
Our commercial services includes below but are not limited to:
- Network Penetration Testing
- Web Penetration Testing
- Wireless Penetration Testing
- Vulnerability Assessment
- Physical Security Testing
- Social Engineering
- Threat Hunt
- SOC
- Network Security Control Testing
- Cloud
- Web Development
- and etc.
Neehack also provide free services that are listed below:
- Threat Intelligence
- World Cyber Threat Map
- Crack Engine
- Offensive and Defensive security tools and etc
Neehack is also partnered with major companies that include Microsoft, IBM, CheckPoint and etc.
Web and Network Penetration Testing SAST/DAST
- Web-Based and Network-Based are the most common types of penetration testing.
- Network penetration testing includes evasion of IPS/IDS, Proxy. Identifying miss-configuration in network-based firewalls or network services such as SSH, FTP, SMTP, RDP and more.
- Web application penetration is a technique for detecting security flaws in web-based applications.
Social Engineering

A threat actor uses social engineering to convince or manipulate internal employees into providing classified data such as login credentials.
Physical Penetration Testing

Physical penetration testing is a form of threat simulation in which a pen tester tries to breach physical barriers to gain access to a company’s infrastructure, building, systems or employees.
Security Audits
An information security audit is an audit on the level of information security in an organization. Within the broad scope of auditing information security there are multiple types of audits, multiple objectives for different audits, etc. Most commonly the controls being audited can be categorized to technical, physical and administrative. Auditing information security covers topics from auditing the physical security of data centers to auditing the logical security of databases, and highlights key components to look for and different methods for auditing these areas.
Neehack Threat Map
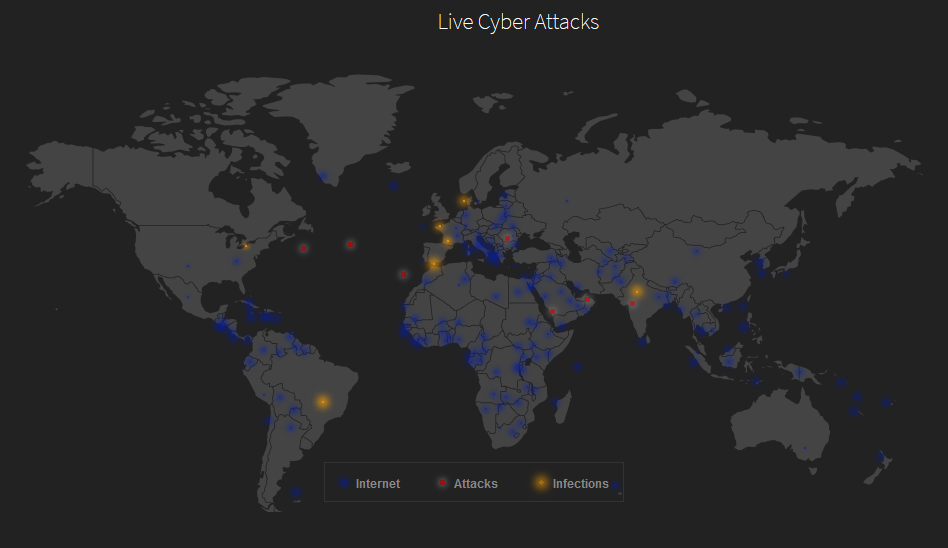
Neehack threat map is a free service that shows live cyber-attack and infections world-wide. For visual preview visit: https://www.neehack.com/map
Contact Us or Get a Quote
- Live chat available at: https://neehack.com/
- Email us at: support@neehack.com
- Call us at: +1 (437)-237-1562
